Blog
Security research, penetration testing walkthroughs, and lessons from the field.
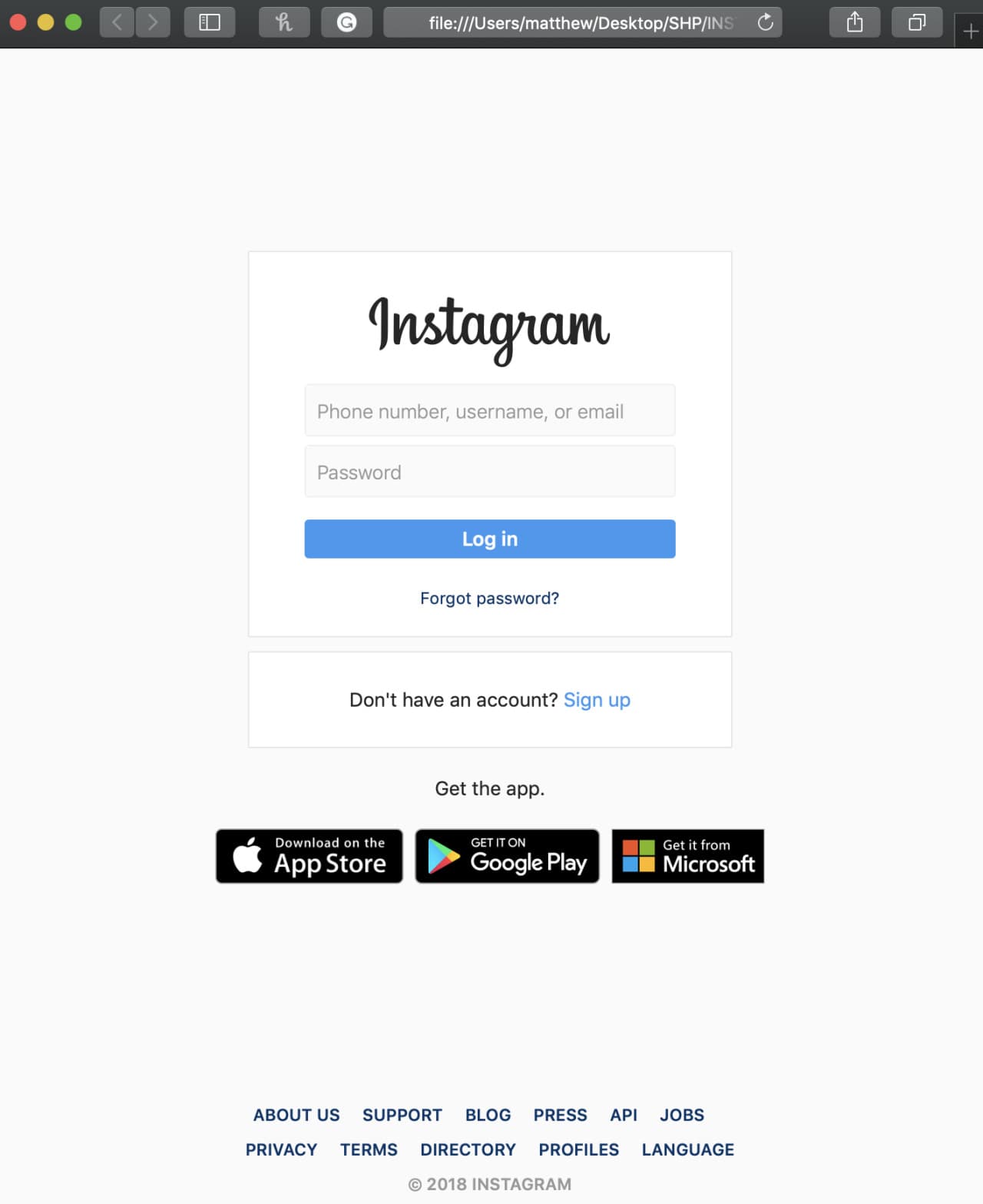
How easy is it to build a phishing page?
A walkthrough of how phishing attacks work under the hood, from cloning a login page to capturing credentials, and what you can do to protect yourself.
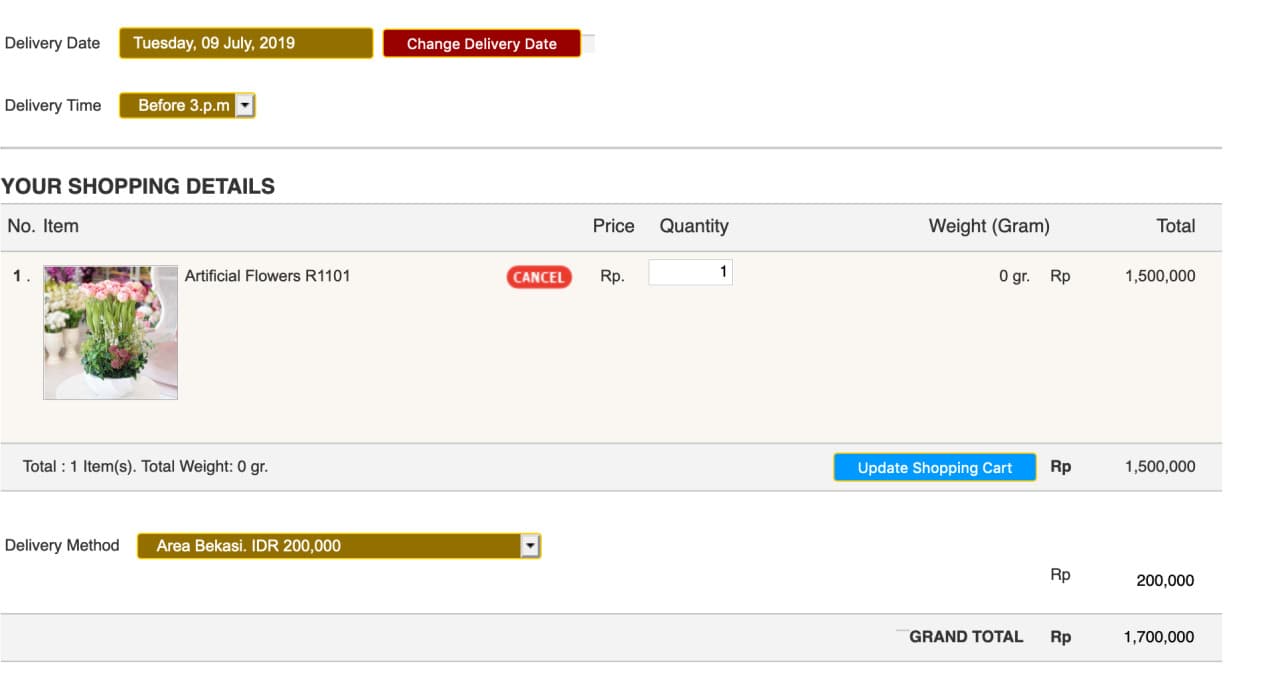
Intercepting HTTP requests with Burp Suite
How Burp Suite can be used to intercept and modify HTTP requests, demonstrated by finding a price manipulation vulnerability on a live ecommerce site.
Why open WiFi networks are a security risk
A real-world demonstration of MAC address spoofing on an open hotel WiFi network, and why you should think twice before connecting to public WiFi.

Automating SQL injection testing with sqlmap
An introduction to sqlmap, the go-to tool for automated SQL injection detection, covering basic usage, database enumeration, and advanced techniques.

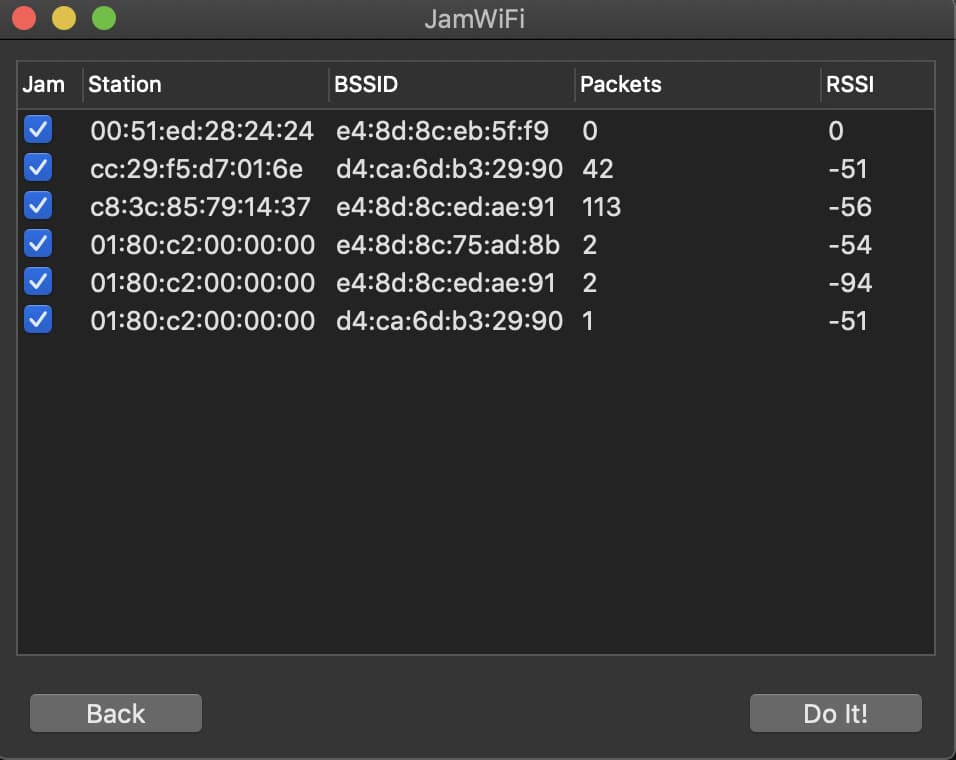
Understanding Evil Twin attacks on WiFi networks
How Evil Twin AP attacks work, from deauthentication packets to fake captive portals, and practical steps to protect your network.